Achieving PCI DSS Compliance: A Start-to-Finish Guide
Learn about the key aspects of PCI DSS and get valuable insights and actionable steps to safeguard sensitive data and maintain customer trust.

For any organization handling cardholder data, adhering to the Payment Card Industry Data Security Standard (PCI DSS) is crucial today. This comprehensive guide will walk you through the key aspects of PCI DSS compliance, providing valuable insights and actionable steps to safeguard sensitive data and maintain customer trust.
We’ll explore:
- An overview of the PCI DSS framework and its 12 core requirements
- The importance of PCI DSS and its benefits to your organization
- Key steps to achieving and maintaining PCI DSS compliance
- Expert tips for a smooth compliance journey and fostering a culture of continuous security
The Context of PCI DSS
When cyber criminals began targeting credit card data in the late 1990s, industry professionals quickly understood they needed to work together to create standards to help protect this sensitive data from would-be attackers. From there, the idea of a credit card security framework was born.
The first version of the PCI DSS framework unveiled in 2001 was representative of cybersecurity frameworks used by a variety of companies in the credit card industry. The most recent version represents a unification of the industry’s technical and operational requirements to protect cardholder data.
PCI DSS standards form a comprehensive cybersecurity framework and outline best practices your organization should implement to protect sensitive cardholder data from being stolen and misused by attackers.
If your organization accepts, stores, processes, or transmits credit card information, you are subject to compliance.
What is PCI DSS?
The Payment Card Industry Data Security Standard (PCI DSS) is a globally recognized set of security standards designed to safeguard sensitive cardholder data.
Developed by five major credit card companies, the PCI DSS framework is essential for businesses that store, process, or transmit credit or debit card information. Compliance with these standards will not only protect sensitive cardholder data, but will also create a sense of trust and credibility among customers and business partners.
Your organization can emphasize how well you meet these compliance standards by completing an assessment from an independent qualified security assessor (QSA) who can certify that your organization’s existing security procedures meet framework requirements. An approved scanning vendor (ASV) can validate if your vulnerability scan practices meet PCI scan requirements.
If you successfully meet those requirements, your organization can receive an Attestation of Compliance report, which you must review each year.
If you are not required to submit a Report on Compliance (ROC), you can complete a self-assessment questionnaire to self-assess how well you’re meeting compliance standards.
Failing to meet PCI compliance standards can have a range of negative consequences including significant financial penalties, potential risk of data breaches, and damage to your brand and reputation.
Requirements of PCI DSS Compliance
The PCI DSS framework represents 251 requirements organized into 12 core areas. These 12 requirements are “controls.”
To achieve compliance you must demonstrate you meet these requirements and successfully pass an assessment from a qualified security assessor.
- Firewall Configurations - The firewall is the guardian of your digital environment. It stands at the gates and blocks any potential invaders from breaking in. A well-configured firewall acts as a first line of defense against unauthorized access, ensuring that only trusted sources have access to your systems. Routinely monitoring these configurations helps keep security measures up-to-date.
- Secure System Passwords - Default vendor supplied passwords are widely known, making them a prime target for cyber attacks. By creating unique and complex passwords, businesses can significantly reduce the risk of unauthorized access.
- Data Encryption - Encryption, hashing, and other forms of data protection make sensitive cardholder information unreadable to unauthorized users. Implementing these methods not only secures data at rest but also during transmission.
- Regular System Updates - Updating and patching up systems on a regular basis helps to eliminate vulnerabilities that could be exploited by cybercriminals. This ensures a more secure environment for cardholder data.
- Use of Anti-Virus Software - Establishing and habitually updating anti-virus software is vital for detecting, preventing, and mitigating threats from malware and other malicious software.
- Data Access Restrictions - Granting users the minimal level of access required to perform their job duties can allow businesses to significantly mitigate the risks of authorized users accessing sensitive cardholder data.
- Identification & Authentication Requirements - Assigning unique User IDs to each authorized user helps ensure accountability and enables effective tracking of user activity for the purpose of maintaining security.
- Physical Access Restrictions - Controlling and monitoring physical access areas where cardholder data is stored, processed, or transmitted is crucial in preventing data breaches, enforcing accountability, and maintaining compliance and a secure environment.
- Password Management - Implementing strong and complex passwords and regularly changing passwords can significantly reduce the likelihood of unauthorized access, ensuring an additional layer of security for your business.
- Data Access Tracking & Monitoring - An incident response plan ensures that your business is prepared to promptly and effectively address any security incidents that may arise. The continuous monitoring and tracking of data access provides an additional layer of security to detect and respond to potential threats in real-time.
- Security Testing Review - Regularly reviewing user access helps ensure that only authorized people have access to cardholder data and minimizes the risk of internal threats. This routine security testing strengthens the overall security by identifying vulnerabilities.
- Security Policy Development - Developing extensive security policies and procedures helps provide a solid foundation for your business’s data security efforts. Regularly reviewing and updating these policies helps ensure they remain aligned with the evolving industry standards.
Why Does PCI DSS Matter?
Compliance with PCI DSS is vital for several reasons:
- Improve Security - As cyber threats brew, a solid PCI DSS strategy can drastically reduce the likelihood of security incidents and financial losses.
- Build Trust and Credibility - In the world of commerce, trust is priceless. PCI DSS compliance demonstrates to customers, partners, and stakeholders that your business is committed to safeguarding their sensitive data.
- Avoid Penalties - Failing to adhere to PCI DSS guidelines can result in exorbitant fines, legal battles, and reputation damage to your business. Prioritizing PCI DSS compliance ensures that your company steers clear of these hazards.
Should Your Organization Be PCI Compliant?
Regardless of the industry, if your organization accepts, stores, processes, or transmits credit card information, you are subject to PCI compliance. Based on the industry you’re in, here are a few ways aligning with the PCI DSS can benefit you.
Retail
Maintain your professional reputation while keeping your clients’ financial data secure.
Healthcare
Cyber-attacks on the healthcare industry are on the rise, so provide your patients with peace of mind with PCI-compliant data security standards.
Nonprofits
Nonprofit agencies process thousands of credit cards per year, so it’s crucial to include PCI DSS compliance standards in your overall security program.
Energy & Utilities
Demonstrate that your company maintains the highest standards for financial data security.
Dining, Travel, & Leisure
Protect your brand and reputation by ensuring you’re protecting your customers’ credit card information.
Internet & Technology Providers
Receive and maintain credit card data with confidence while protecting your brand and company reputation.
Financial Services & Insurance
As heavily-regulated sectors, it's imperative you demonstrate that you have the right security protocols in place.
Professional Services
Safeguard your clients' credit card information and protect your brand and reputation.
Other Industries
Include PCI DSS compliance as your part of insurance plans and protection against data theft.
Want to accelerate your PCI DSS compliance process?
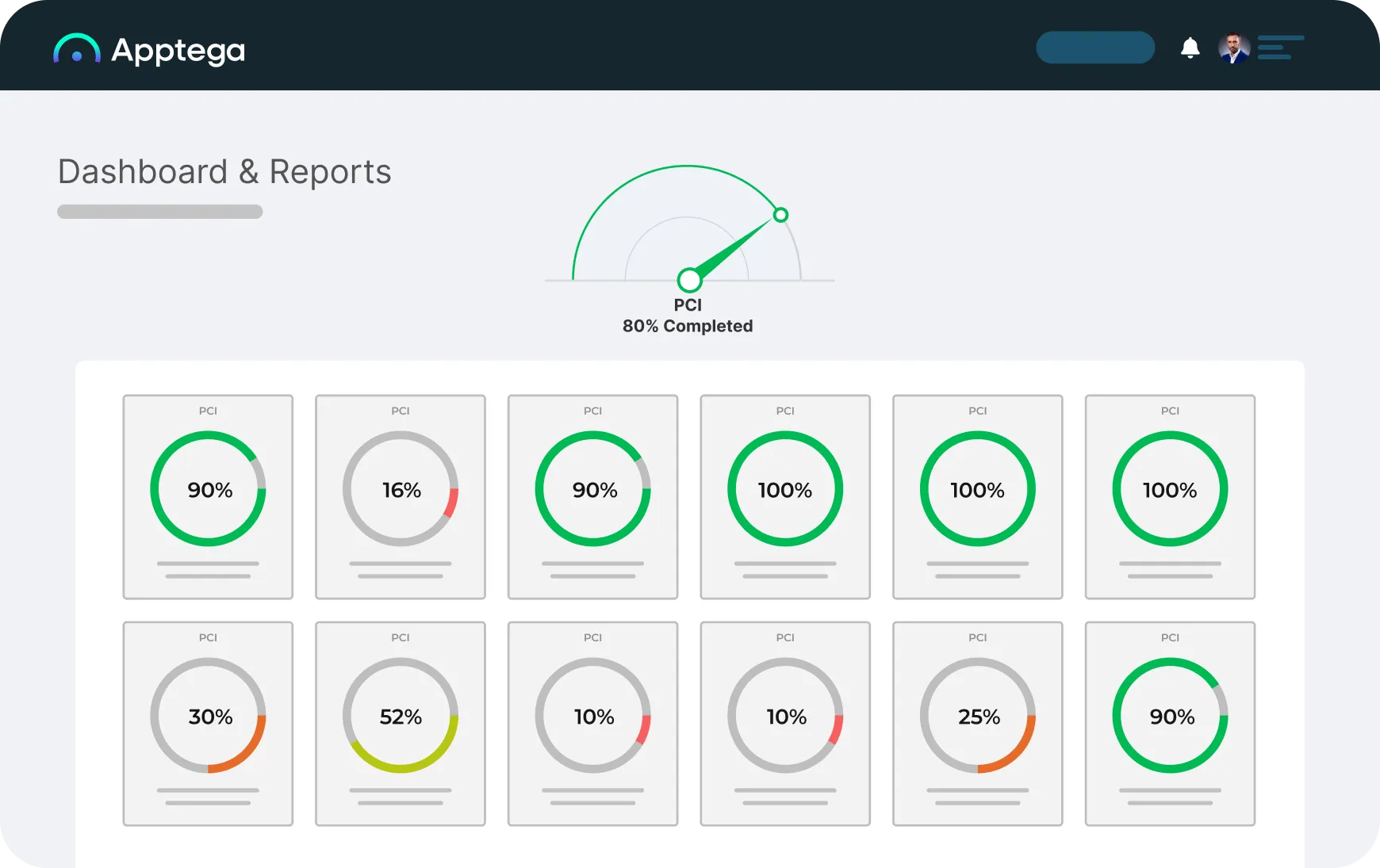
With Apptega’s PCI DSS compliance software, you can use streamlined questionnaires, integrations to your sources of truth, and framework crosswalking to run through PCI assessment and audit like a breeze.
Understanding PCI DSS 4.0
Mandatory since April 1st, 2024, PCI DSS 4.0 is the latest version of the PCI DSS framework, which focuses on improving the overall security position of organizations by adapting to the evolving environment.
Some notable new features and updates of PCI DSS 4.0 include:

To accommodate the various types of businesses and security environments, PCI DSS 4.0 offers more adaptable security solutions.

Recognizing security as a continuous process, PCI DSS 4.0 encourages ongoing monitoring and risk assessment to maintain payment security.

MFA requires users to provide two or more verification factors, tokens, or biometrics, making it more difficult for unauthorized users to access sensitive cardholder data.

Continuously emphasizing the need for ongoing risk assessment ensures that businesses stay proactive in their security efforts and adapt to the changing threat environment.
Check out our recent webinar with Brendan Cassette, Technology and Cybersecurity Analyst at VISTRADA, where he does a deep dive into PCI DSS 4.0, the latest iteration of this essential standard.
PCI DSS Compliance Levels
All PCI merchants are classified into one of four compliance levels. These levels are based on credit or debit card transaction volume during a 12-month period. This includes the transaction volume for all credit, debit, and prepaid transactions.
Level 1: PCI DSS merchants with over 6 million transactions per year
Level 2: PCI DSS merchants with between 1 million to 6 million transactions per year
Level 3: PCI DSS merchants with between 20,000 to 1 million transactions per year
Level 4: PCI DSS merchants with less than 20,000 transactions per year
Each level has specific requirements and validation processes, ensuring that businesses can implement appropriate security measures based on their transaction volume.
PCI DSS Compliance: A Step-By-Step Guide
Although PCI DSS controls the PCI DSS Framework standards, individual credit card companies can direct their own compliance measures. Therefore, businesses should adhere to the payment card company’s requirements when pursuing compliance.
However, the following steps can serve as a guideline to help organizations navigate their PCI DSS journey.
- Determine Scope: Identify and document the devices, systems, components, and networks that store, process, or transmit cardholder data in order to make them subject to PCI DSS requirements.
- Assess Compliance: Evaluate your businesses current compliance status by going through a thorough assessment addressing each PCI DSS requirement. This may involve actions like vulnerability scans, penetration tests, and reviews of security policies and procedures.
- Complete Reports: Finalize all compliance reports needed, either independently or with the help of a professional. Ensure the reports accurately document all controls you have implemented and their effectiveness.
- Submit Self-Assessment: Fill out your self-assessment questionnaire, AOC, Report on Compliance, Approved Scanning Vendor, and any other required documentation to your requestor for validation.
- Address Gaps: Amend any gaps identified or areas of non-compliance by implementing appropriate measures. Following these updates, conduct a reassessment and update your compliance reports to reflect your progress.
How to Map PCI DSS to the NIST Cybersecurity Framework
Many organizations in a variety of industries rely on the National Institute of Technology’s (NIST) Cybersecurity Framework to develop their cybersecurity programs and then mature them over time. The NIST framework provides a solid foundation for cybersecurity, and coupled with PCI DSS, they share common goals—to protect sensitive data and improve data security.
Mapping Made Simple
If you already have the NIST Cybersecurity Framework in place, you may be curious to know if you can map PCI DSS to it? The answer is, yes! Aligning the two can help you align your organization’s overall cybersecurity and compliance objectives and create a better understanding the effectiveness of your security procedures.
Apptega's Framework Crosswalking feature, known as Harmony, allows you to automatically crosswalk and consolidate all shared controls, sub-controls, resources and activities across multiple frameworks within your program. With this powerful capability, you can significantly improve efficiency and reduce overhead.
How to Automate the PCI DSS Compliance Process with Software
Advances in technology have made it possible to use software solutions to simplify and streamline the PCI DSS compliance journey. By utilizing PCI DSS automation tools like Apptega, organizations and security providers can:
- Monitor and manage their security posture in real-time
- Automate evidence collection and reporting to demonstrate compliance
- Detect potential threats and vulnerabilities before they become critical
- Streamline compliance with other frameworks, thanks to overlapping controls and requirements.
Apptega’s platform helps businesses by centralizing all aspects of PCI DSS compliance, from the initial assessment to becoming audit-ready. By choosing a reliable, end-to-end solution, you can focus on growing your business (by delivering your security services in service of this or any other framework) while confidently maintaining the highest level of data protection and customer trust.
PCI DSS FAQs
PCI DSS is an abbreviation for Payment Card Industry Data Security Standards. These standards are technical and operational requirements established by the PCI Standards Council (PCI SSC) to protect cardholder data. Any organization that accepts stores, processes, or transmits credit card information must meet PCI DSS standards. There are also requirements that directly affect software and app developers (Payment Application Data Security Standard (PA-DSS)), as well as those that create devices used for credit card transactions (PIN Transaction Security (PTS) requirements).PCI DSS sets six core goals achieved through 12 individual requirements. While PCI SSC sets the security standards, each credit card brand determines compliance, validation levels, and enforcement. PCI DSS compliance is assessed by qualified security assessors (QSAs). Approved scanning vendors (ASVs) validate PCI DSS vulnerability scan requirements. The first version of PCI DSS debuted in 2001, representing best practices and frameworks in use by the industry’s major credit card companies. The most current version is v3.2.1.
PCI SCC is an abbreviation for the Payment Card Industry Security Standards Council. In 2006, American Express, Discover, MasterCard, Visa, and JCB International united to found the council. As a result, each credit card company includes PCI DSS in their individual data security compliance requirements. PCI SSC guides creation of PCI DSS with a mission to “enhance global payment account data security by developing standards and supporting services that drive education, awareness, and effective implementation by stakeholders.” Learn more about PCI SSC at https://www.pcisecuritystandards.org/about_us.
Cardholder data, according to PCI SSC, is at a minimum the full primary account number (PAN) of a credit card or the full PAN along with any of these: cardholder name, expiration date, or service code. PCI SSC also requires protection of security-related information including sensitive authentication data such as the magnetic stripe data, chip data, PINs, PIN blocks, card validation codes, card validation values, and more.
Being PCI compliant means adhering to the Payment Card Industry Data Security Standard (PCI DSS) requirements, which involves implementing strong security measures to protect cardholder data and maintain a secure environment for processing, storing or transmitting credit card information.
Any organization that accepts, processes, stores, or transmits credit card data is required to comply with PCI DSS standards, including service providers, merchants, financial institutions, and other entities involved in the payment card transaction process.
Yes. As with many cybersecurity standards, if your organization uses third-party processors, PCI DSS applies to each of them. Utilizing third-party processors that are PCI DSS compliant helps reduce your risks for an potential data breach. While you should always ensure third-party compliance, don’t stop there. Always look down your supply chain. Do your vendors use other vendors that may access you cardholder data? If yes, you will want to make sure they’re compliant too to help reduce your risks and exposures.
The primary purpose of PCI DSS is to protect sensitive cardholder data and reduce the likelihood of a data breach and risks associated with the loss of credit card information. Payment Card Industry Data Security Standards outline how you can prevent potential attacks or breaches, how these attacks can be detected within your systems, and what you should do in the event of a breach. In addition to reducing risks, being PCI DSS compliant builds trust with your customers, key stakeholders, and vendors. It demonstrates that you are taking proactive and industry-approved actions to keep their sensitive data safe.
Businesses should review their PCI DSS compliance at least once a year and perform regular vulnerability scans, penetration tests, and risk assessments to ensure ongoing adherence to security standards.
Non-compliance with PCI DSS may result in fines ranging from $5,000 to $100,000 per month, increased transaction fees, reputational damage, legal action, loss of customer trust, and potentially losing the ability to accept credit cards.
Non-compliance with PCI DSS may result in fines ranging from $5,000 to $100,000 per month, increased transaction fees, reputational damage, legal action, loss of customer trust, and potentially losing the ability to accept credit cards.
Still have a question?
Get in touch with us and we would be happy to help.
Ready to get started?
Request a no-risk 14-day free trial to see how you can create a sticky compliance-as-a-service offering with Apptega.
.svg)






